Introduction: the “Salesforce security” moment that matters
If you’ve seen alarming headlines about a massive Salesforce security breach, you’re not alone. In early October 2025, a hacker collective claimed it stole nearly 1 billion records from companies’ Salesforce environments and launched a leak site to extort victims. Salesforce said its own systems weren’t breached—the attackers largely went after customer instances and third-party integrations that connect into Salesforce. Reuters+1
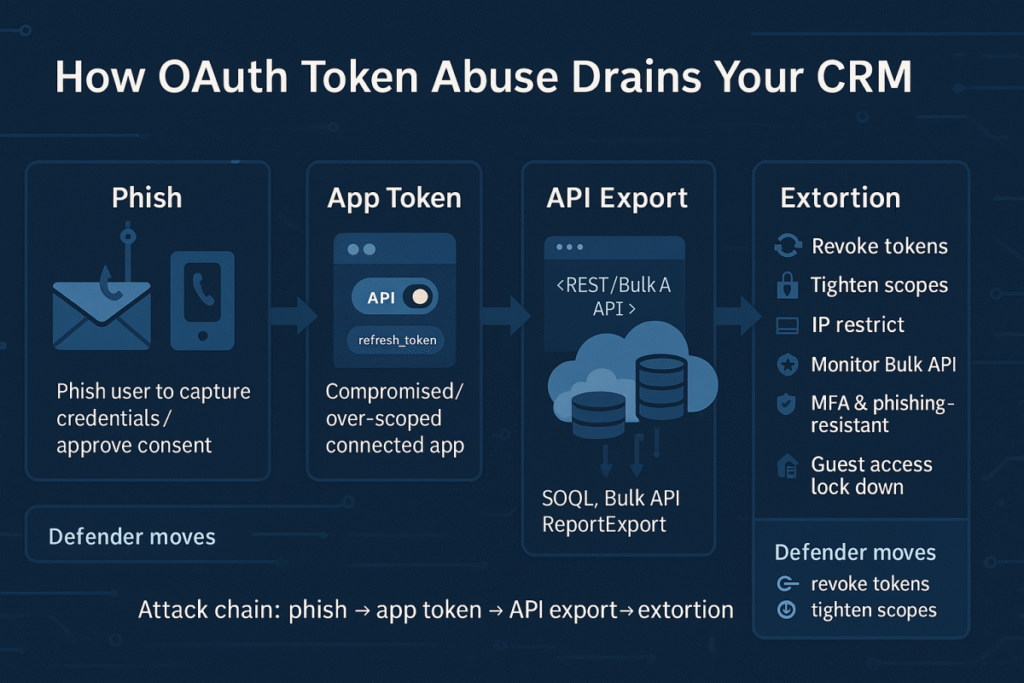
Weeks earlier, Google’s Threat Intelligence team had already warned about a campaign abusing compromised OAuth tokens from a third-party app (Drift by Salesloft) to pull data from Salesforce customer orgs—a reminder that modern CRM risk often lives in the ecosystem as much as the platform. Salesforce published a status note the same day to guide impacted customers. Google Cloud+1
This post cuts through the noise: we’ll clarify what’s known so far, compare the types of incidents being conflated in headlines, and give you a field-tested playbook to harden your Salesforce footprint—today.
The story so far
- Claimed scope: Hackers say they exfiltrated ~1B records from organizations using Salesforce, not from Salesforce’s core infrastructure. Salesforce denies a breach of its own systems. Reuters+1
- Likely pathway: Multiple investigations point to social engineering (vishing) plus stolen or abused OAuth tokens from connected apps, enabling API-level data pulls from customer orgs. Reuters+1
- Confirmed victims (examples): Several companies have acknowledged related data theft tied to the Drift/Salesloft integration, reinforcing the third-party app angle. Tech Radar
- Active extortion: A new leak site is pressuring victims—evidence that the campaign is ongoing, organized, and monetization-driven. UpGuard
Bottom line: say “Salesforce-related breaches,” not “Salesforce itself was breached,” unless you’re describing a specific, verified platform-side incident. Precision keeps stakeholders calm—and focused on the right fixes. Reuters
Comparison: one headline, three different failure modes
| Vector | What it is | How it hits Salesforce customers | Signals you’ll see | First response |
|---|---|---|---|---|
| Customer org compromise | Attackers get valid creds or session for your Salesforce tenant (phishing/vishing/MFA fatigue). | API exports, data report pulls, mass queries; often low-noise if tokenized. | Unusual API consumption, high-volume SOQL queries, odd login geography. | Reset users, invalidate sessions, force MFA reset, event log review. |
| Connected-app/OAuth abuse | Stolen or over-scoped OAuth tokens on apps that connect to Salesforce. | “Legitimate” app pulls huge data without tripping basic auth alarms. | New/unknown connected apps; abnormal token use outside expected IPs. | Revoke tokens, audit scopes, rotate app secrets; review IP relaxations. Google Cloud+1 |
| Misconfiguration exposure | Public/guest access accidentally reveals private objects/fields on Experience Sites or reports. | Anyone can browse sensitive data without logging in. | External discovery (bug hunters, journalists), Google indexing leaks. | Disable guest perms, review sharing, run site scanner, fix profiles. Krebs on Security+1 |
Historical context: Salesforce-adjacent incidents aren’t new. In 2022, an incident at Heroku (owned by Salesforce) led to OAuth token theft involving GitHub integrations—an early glimpse of the downstream risk of tokens and integrations. Heroku+1
Key insights you won’t get from generic “breach” takes
1) CRM is the crown-jewel data lake for attackers
Salesforce concentrates prospect, customer, and support data—exactly what fuels targeted phishing and fraud campaigns at scale. Once pulled, it’s easy to monetize and hard for victims to “revoke.” This is why adversaries favor “legitimate” channels like OAuth/API over noisy web scraping. TechRadar
2) OAuth tokens are today’s skeleton keys
The 2025 wave shows how a compromised connected app can quietly open the door to your org, regardless of user MFA. In practice, many tokens are long-lived, broadly scoped (e.g., api, refresh_token), and allowed from any IP—perfect for off-hours bulk exfiltration. Google’s write-up on the Drift/Salesloft incident is the blueprint of this pattern. Google Cloud
3) Misconfig isn’t “old news”—it’s evergreen
Even in 2023, researchers were finding sensitive data exposed via guest access on public Salesforce sites. Those lessons still apply: least privilege on guest profiles, object/field-level checks, and a habit of testing sites as an unauthenticated user. Krebs on Security
4) Language matters for incident comms
C-suite panic spikes when they hear, “Salesforce was breached.” Precision protects trust. Reserve that phrasing for official platform advisories; otherwise, describe the actual vector (customer instance, third-party OAuth, or mis config). Keep a link handy to Salesforce’s own advisory hub. Salesforce Security
A practical hardening checklist (use today)
Identity & sessions
- Enforce MFA (prefer phishing-resistant methods for admins and integration owners).
- Require High Assurance for sensitive actions; shorten session timeouts for API users.
- Review login IP ranges and login hours for service accounts/integration users.
Connected apps & OAuth
- Inventory all connected apps; kill what you don’t need.
- Right-size scopes (avoid
refresh_tokenunless essential; prefer narrow, read-only scopes). - Enforce IP restrictions or Mutual TLS on integration paths where feasible; avoid “Relax IP restrictions” unless you truly must.
- Rotate consumer secrets regularly; alert on token issuance outside change-window hours.
- Monitor for new connected apps or changes to existing ones (approval workflows + notifications). Google Cloud
Data governance
- Tag and minimize high-value fields (PII, commercial terms, support case content).
- Use Transaction Security Policies (or equivalent) to throttle/deny bulk exports.
- Limit who can create reports/exports; alert on unusually large report runs.
Monitoring & response
- Turn on Event Monitoring / Shield and stream events to your SIEM; alert on:
- Unusual Bulk API/REST query volumes
- Tokens used from new geographies
- Sudden spikes in ReportExport events
- Practice a 72-hour CRM exfil drill: revoke tokens, reset sessions, rotate secrets, notify legal/comms, and seed targeted phishing warnings to affected contacts.
Experience Cloud & guest access
- Audit guest user profiles for object/field-level access.
- Crawl public sites as an anonymous user; check that sensitive data isn’t indexed.
- Follow Salesforce guidance for locking down guest permissions ahead of releases. Trailhead
Keep a steady pulse
- Subscribe your security team to Salesforce Security Advisories; treat them like change windows for your controls.
Mini-playbook: if you suspect Salesforce data theft

- Contain
Revoke all connected-app tokens; temporarily disable risky apps and integration users. Force logout for all users; reset high-risk accounts. Salesforce Trust Status - Scope
Pull Event Monitoring logs (API, Bulk, ReportExport). Identify objects/fields touched and volume of records. If you use Drift/Salesloft, confirm whether OAuth tokens were present and when they were used. TechRadar - Eradicate
Rotate app secrets; tighten scopes; re-enable integrations one by one under monitored change. Validate IP policies and MFA on integration paths. - Notify
Prepare clear, accurate language (vector, timeframe, data categories). Avoid saying “Salesforce was breached” unless you’re citing an official platform advisory. Link to the relevant third-party incident notes if applicable. TechRadar - Harden
Implement the checklist above; add detections for the exact patterns you observed.
Frequently asked questions
Was Salesforce itself breached?
Salesforce says there’s no evidence its core systems were breached; the current wave targets customer instances and integrations. Reuters
What about the Drift/Salesloft situation?
Google’s threat intel describes attackers using compromised OAuth tokens linked to the Drift app to access Salesforce orgs; Salesforce posted an advisory for customers using that integration. Google Cloud+1
Isn’t this just like the 2022 Heroku incident?
It’s a different event, but both highlight the risk of tokens and connected ecosystems around Salesforce. Treat token security as a top-tier control. Heroku
Could misconfiguration still leak my data?
Yes—especially via guest access on Experience Cloud sites. Periodic audits are essential. Krebs on Security
Conclusion: treat CRM like a data supply chain
The most important lesson of this “Salesforce security” news cycle is that your risk is shared across people (social engineering), process (change control), and platforms (connected apps). Headlines may blur those lines; your defense cannot.
Focus on:
- Killing excessive OAuth scopes and tokens
- Monitoring for abnormal exports
- Hardening guest access
- Rehearsing containment
Do those relentlessly, and you’ll turn a noisy week of breach chatter into a catalyst for durable CRM resilience. For ongoing platform updates, keep an eye on Salesforce Security Advisories and credible threat-intel briefings. Salesforce Security+1
CTA: What should you do next?
- Run a 60-minute Salesforce risk sprint today: inventory connected apps, revoke stale tokens, and set alerts for large exports.
- Share this guide with your RevOps and Security leads—then book a joint tabletop exercise this month.
- Want deeper coverage? Explore our internal resources on OAuth hardening, event monitoring queries, and guest-user lockdown (link to your related posts).
Sources worth tracking
For evolving details on the current campaign and remediation guidance: Reuters, TechCrunch, UpGuard, Google Threat Intelligence, Zscaler’s disclosure, and Salesforce’s own advisories/status notes.
Read more: Salesforce Trust Status+5Reuters+5

